I am still hearing about AV/IT convergence as if it’s a new thing. As far as I can tell, it’s a done deal, and it has been going on for a while. I’m a bit perplexed about this continuing conversation because my first project when I came to AVIXA (then InfoComm International) was to help develop a course in (guess what?) AV/IT convergence.
That was 12 years ago, and the three-day class covered AV/IT integration from start to finish. That means that, more than a decade ago, AVIXA was training AV practitioners so they’d know how to do things like talk to IT personnel about their systems, estimate their bandwidth requirements, understand the Open Systems Interconnection (OSI) layers and IP protocols, design and integrate a converged system, and harness the myriad of opportunities that present themselves with networked systems.
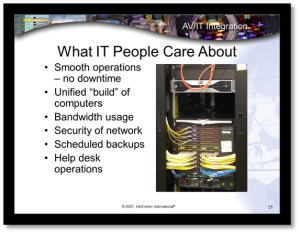
Look at Figure 1, a slide from that 12-year-old course, describing some of the things that keep IT professionals up at night. Even back then, we knew that network security was a concern for those who were responsible. The notes that accompany the slide emphasize the point. “The bottom line for IT: Avoid downtime. Don’t lose data. Operate securely.”
Audiovisual systems are on the network. Integration and convergence are happening—no, they’ve happened. We have a responsibility to the enterprise whose networks we’re on to make sure our AV systems are not enabling intrusions…that we’ve done everything we can to understand what’s at stake, and taken steps to mitigate the risk for the entire enterprise. That lofty goal gets harder by the day.
There are many, many standards and practices that have been put in place through the years to lock down vulnerabilities that hackers could exploit and to prevent breaches, and many cybersecurity firms provide 24/7 intrusion detection. That’s great…but most of the standards and guidance deal with the network itself, not with the systems being put on the network.
You can try to pull together something yourself by researching all the standards that IT has been using for years, but the information isn’t AV-system specific. You can glean some relevant information, but there are gaps, and a lot of information is not germane to what our systems require.
A new AVIXA publication, Recommended Practices for Security in Networked AV Systems, provides help for AV systems integrators, technology managers and anyone else interested in guidance for improving networked AV system security. AVIXA has worked with subject-matter experts to aggregate the recommended practices (RP) you have to follow, regardless of the size of your organization.
The advice is easy to understand and very practical. The RP urge you to identify your risks and the gaps in your security, and they provide a host of other tangible ways to be better at protecting your AV system from threats. Did you know it’s estimated that 50 percent of the passwords used today are still the word “password”? It’s hard to believe, but there it is. Password protection is still an issue, and changing passwords is a recommended practice that should not be ignored.
There are more than 20 actionable items for AV professionals to implement; additional steps you can take; use cases for conferencing, smart buildings and IoT systems; and streaming media to help illustrate the considerations specific to each application.
Security requirements can vary greatly, based on the purpose of the system. Therefore, the RP take great care to provide steps that can be adapted to form a baseline for solid network-security maintenance.
You might be surprised to know how many breaches have happened through third-party contractors. The threat is real and growing. A Global Security Report published by Trustwave in 2013 estimates that 63 percent of intrusions are caused by third-party contractors. Target stores are a case in point.
In the US, the retail chain Target was hacked in 2014. The hackers stole the data for more than 40 million credit cards, and the personal data of more than 70 million customers. It was determined that the company providing HVAC services had been hacked and, using stolen credentials, the hackers tunneled into Target’s other corporate systems network. As if that wasn’t bad enough, Target was indeed warned of the intrusions, but it ignored them. The company lost an estimated $420 million, along with the trust of many customers, by not following the proper guidelines. Protect yourself from this kind of unnecessary risk. Don’t be a target…or a Target.
Although a secure network is something of a moving target, requiring diligence and ongoing effort, we’d all be wise to learn a lesson from the massive breaches that could have been prevented. Wouldn’t it be great for our industry to set an example for maintaining a secure system? If you really want to impress the IT world, let them know that you have followed your industry’s RP for network security. Don’t wait for them to give you their security policies—show them yours.
And, of course, be realistic. You are not immune. It’s not a matter of if you are attacked, but, rather, when.
If you were to do a gap analysis of your networked AV system today, what would you find? Can you show your clients that you have their best interests in mind, and that you have taken the necessary steps to mitigate the risk of an intrusion? Don’t let your AV system be the bad guy.
More information about other AVIXA standards and Recommended Practices for Security in Networked AV Systems can be found at www.avixa.org/standards. AVIXA Premium and Elite members can download the RP publication for free.
